Photo: A comprehensive cybersecurity strategy begins with the hardware and supply chain.
Hardware Security
According to a 2019 survey by Dell and Forrester, hardware- and silicon-level exploits are a pervasive threat.
Nearly two-thirds (63 percent) of companies have experienced a data compromise or breach within the past 12 months due to an exploited vulnerability in hardware- or silicon-level security.
The survey also found that most hardware security initiatives implemented by organizations are ineffective.
While the majority of organizations reported hardware and endpoint security measures as their top security priorities for the coming year, when asked specifically about hardware-level defenses and supply chain protections, they admitted they weren’t properly prepared to address vulnerabilities at these levels.
Perhaps most concerning is that the survey found that organizations struggle to prevent or address the damage sustained by these attacks. They’re turning to hardware security vendors for help, but just 27 percent of organizations surveyed are satisfied with vendor performance.
All this to say: securing the underlying hardware of your server or workstation demands increased attention.
Hardware attacks are often executed during manufacturing or by injecting modified, malicious components or bogus electronic parts into the hardware supply chain.
So, not only could your sensitive data potentially be deleted, altered, or stolen, but the same hardware on which you depend to protect your system could be an unverified, unprotected fake, which not only jeopardizes the security of your system but could also cause a catastrophic failure in the field.
Common hardware attack vectors include:
- Counterfeit electronic parts
- Manufacturing backdoors and supply chain
- Hardware Trojans
Standard preventative and mitigatory measures for hardware attacks include:
- Disabling unused hardware
- Utilizing hardware-based encryption
- Implementing anti-tamper designs
- Thoroughly inspecting and comparing your hardware
- Staying abreast of the latest counterfeit reports
You can also significantly reduce your risk of a hardware-based attack by buying from a computer manufacturer that purchases its supplies from original equipment manufacturers (OEMs), original component manufacturers (OCMs), authorized distributors, and whose products are made in the USA, TAA-compliant, and protected by supply chain security, supplier quality, and counterfeit protection policies and programs.

Photo: Protecting the mediatory layer between your hardware and software is just as essential as protecting the other layers.
Firmware Security
Firmware vulnerabilities are up 750 percent since 2016. Even in just one year, from 2018 to 2019, discoveries of firmware vulnerabilities skyrocketed by 43 percent.
We know we’re throwing tons of numbers at you, but it’s vital to drive home the gravity of establishing holistic security.
Check this one out:
By 2022, 70 percent of organizations that do not have a firmware upgrade plan in place will be breached due to a firmware vulnerability.
If this sounds like your business or organization, it might be time to put a plan in place sooner rather than later.
After all, good firmware is secure firmware.
Common firmware attack vectors include:
Firmware attacks are executed by pushing malicious software into lower-level code. Once implemented, this code can:
- Change or destroy existing firmware
- Target your operating system (OS)
- Penetrate applications installed on your computer
Intel’s Platform Firmware Resilience (PFR) is an emerging solution that helps protect your server’s firmware and validate its integrity. Other solutions include securing your USB ports and staying abreast of the latest firmware updates from manufacturers.
Protecting your firmware, and any other cybersecurity protections you have to test, implement, and manage, is a lot of work. Of course, you could just work with a trusted computing manufacturer that customizes BIOSes and handles all this for you from the moment you start configuring your system.
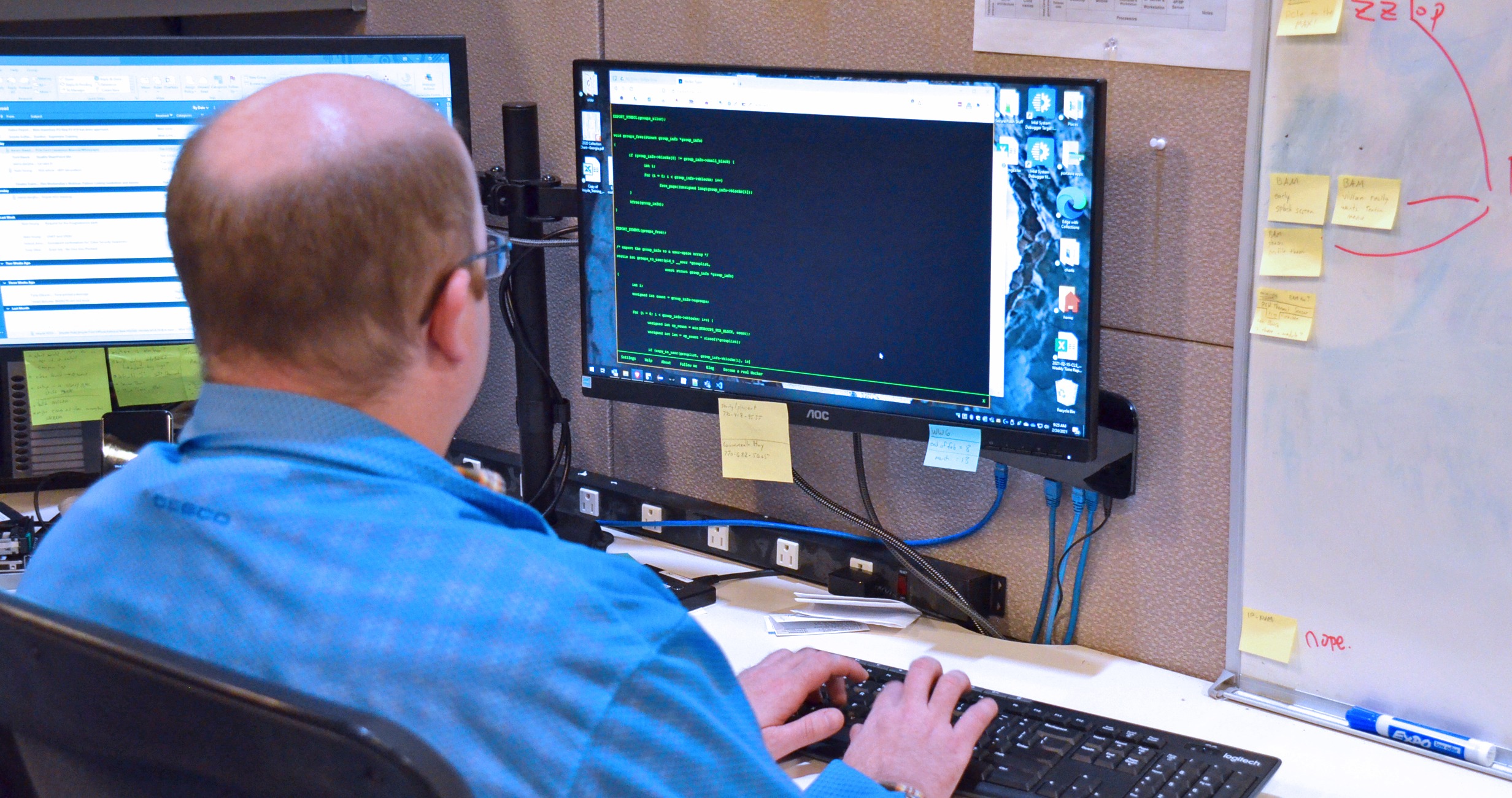
Photo: Yes, hardware security and firmware security are hot topics right now, but lest we forget to keep our eyes on software security as well.
Software Security
Due to the COVID-19 pandemic, total cybercrime is up 600 percent.
Sixty-nine percent of organizations don’t believe the threats they’re seeing can be blocked by their antivirus software.
In April 2020, Google blocked 18 million daily malware and phishing emails related to the novel coronavirus.
Roughly 230,000 new malware samples are produced every day – and this is expected to increase.
Business email compromise (BEC) scams, which frequently use spear-phishing attacks, cost organizations $676 million in 2017.
Ransomware attacks worldwide increased by 350 percent in 2018.
Malware and web-based attacks are the two most costly types of attacks. Companies have spent an average of $2.4 million in defense.
And just one more statistic for good measure: more than 18 million websites are infected with malware every week.
Hardware and firmware may be receiving some newfound attention as potential attack targets, but upper-layer software is still vulnerable and susceptible and demands the same amount of focus. It’s important that we don’t neglect it because of the current spotlight on the others.
Common software attacks include:
Traditional antivirus software is a must-have, of course, but protecting software from exploitation goes beyond mere antivirus programs.
At the end of the day, encryption, secure code signing, and even old-fashioned measures, such as strong password management, remain effective when executed correctly, and multi-factor authentication is the new special-character password.
Other software security protections include:
- Sanitizing inputs to prevent SQL injections
- Using load balancers and IP banning services
- Educating and training employees on browsing secure websites, email-based malware tactics, and effective password management
- Monitoring for changes in software supply chain elements
Services like LastPass can also help you and your business or organization manage your passwords securely and intelligently.
Did you know that, in 43 percent of password-guessing attempts, hackers gain entry just by typing in the username in the password field? It’s just that easy for them. Easily guessable passwords are sensitive-data gold mines served up to hackers on silver platters.
Change the passwords, complicate them, and store printed paper copies only. This strategy is not ideal, we know, but at least hackers, once in your system, won’t be able to view your passwords in any documents you may have stored them in.
Lastly, buying from a trusted, reputable computer manufacturer that partners with leading cybersecurity companies and incorporates leading technologies – such as Star Lab’s Titanium Security Suite – can take a lot of the testing, implementation, management, and pure guesswork out of the software security equation for you.

Photo: Working with caring, passionate engineers who emphasize the security of your servers and workstations will save you time, money, and headaches.
Conclusion: Secure Your System with Trenton
Trenton Systems looks at cybersecurity holistically, focusing on hardware, firmware, and software protections. It’s why we:
- Partner with leading software security companies like Star Lab and FUTURA Cyber for Titanium Security Suite and FIPS 140-2 self-encrypting drive management, respectively
- Customize our BIOSes to add security tweaks and enhancements
- Employ Intel PFR, Intel SGX, Intel TME, and related technologies
- Have a Counterfeit Protection Program (CPP) in place
- Perform supplier quality surveys
- Enforce strict revision control
- Pride ourselves in designing, manufacturing, assembling, integrating, testing, and supporting our cybersecure computing solutions in the USA
- And a host of other processes, procedures, and practices you can learn about in our Master List of Trenton Systems’ Cybersecurity Advantages & Solutions
If you’re interested in acquiring a cybersecure, made-in-USA, high-performance computing solution, manufactured in a secure United States facility, look no further than Trenton Systems.
We’ve got you covered – to the core.




















.png#keepProtocol)











-1.png#keepProtocol)